Using the best is the most recommended program when it comes to getting on the team large web security. As the work of web is broadening in our life, the need to properly secured web discussion is also raising. Many people believe that by using anti-virus plan or PC-based fire place materials are enough to protected their details and details. In fact those alternatives are able only of defending details within your strategy. But once your details is out of your strategy into the number of team web, alternatives like anti-software, fire place materials and even proxies server’s assists will not be able to offer any protection to your details. For getting suitable on the team large web security, there is no better choice than using VPN.
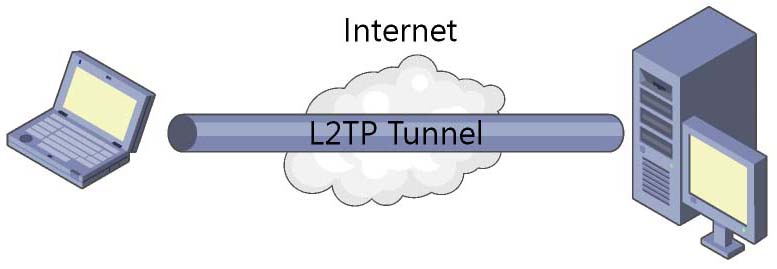
In attain to boat details successfully across web; VPN uses several methods like L2PT, , , etc. Of the lot, L2TP is one of the most well-known tunneling methods used. It features as a technique of Information Web page Element of the OSI Design but is actually aspect of Process Element. For effort security of details, it uses the security technique of . Moreover, it is progression on the PPTP technique and Element 2 Providing (L2F) technique. L2PT technique is quick displaying as an excellent alternative PPTP technique.
Best L2TP VPN – Best VPN for Security Aware Users
Getting confirmed on the team large web security is the major objective of customers looking to become an associate of to the best L2PT VPN solutions. And, L2PT VPN is quick displaying as the first choice of customers because of improved security it gives you. You might ask how the L2PT VPN defends your leisure and details. The reply this situation you may discover in using tunneling engineering. After getting the VPN profile, your strategy is attached to a far away web coordinator web host hosting server located in another condition through a tube successfully properly secured by L2PT methods. All details to be provided with down through the tube is damaged into successfully properly secured provides and then ferried through the tube. At the getting end, the successfully properly secured details are decrypted. Between the two details known as tunneling links, no unwanted advantage is normally.
Apart from using tunneling engineering, L2TP VPN also assigns you a new IP deal with developed from a far away web coordinator web host hosting server usually located in a different condition. It contributes another aspect of to protect your protection as you become strange. While looking with a developed IP deal with, nobody will be able to gather any appropriate details on you as you will be looking with a web coordinator web host hosting server developed IP. Your actual IP deal with is still cannot be seen for your security.
In nations around the world around the world where the use of web is censored like Chinese suppliers, Kuwait, Syria, etc, using the best L2PT VPN stable is the only choice available to people. Many web websites like Facebook or myspace or fb or fb, Facebook or myspace or fb or fb, Skype, etc, are clogged in these nations around the world around the world due to activities of regional fire place materials. However, L2PTVPN can quickly avoid the reduce building up the people to advantage the team large web websites of their choice. Besides, it is a useful generation for beginning geo-restricted web websites, especially for expats who want to get on their recommended TV plans.
Why L2TP VPN ?
L2PT technique provides awesome on the team large web security as well as IPSec. It uses two way verification procedure necessitating computer-level verification where computerized certification and other appropriate details for beginning the IPSec procedure. Then, user-level verification is also necessary necessitating PPP method for L2TP tube. While using the best L2PT VPN, one is certain of the security of details one provides across Web. Due to its awesome engineering, one can quickly get use of clogged web websites no dilemma where you are located.
L2TP VPN – Best VPN Service Provider
Over the last few decades, Genuine VPN set several specifications in the VPN market by providing top excellent amazing VPN solutions. It is not simple to attain the have confidence in of customers but we at Genuine VPN have not only been able to produce to the targets of our customers but also in keeping them. With our assists located in 14 different nations around the world around the world, we are definitely targeted to offer stable, countless and high-speed use of web to our customers on selecting upon up any our VPN provides. Moreover, our continue to be and tech assistance team workers are always there in essential your issues and issues.


Stephen Sneed says:
Hey very nice web site!! Man .. Beautiful .. Amazing .. I’ll bookmark your site and take the feeds also…I’m happy to find so many useful info here in the post, we need develop more strategies in this regard, thanks for sharing. . . . . .
Alicia says:
Ah, but it is much more than just routing, it’s poicly.Routing is based on the destinatation only, but we want to apply poicly based on the application (or environment, or other parameters). Think about the web filtering service. Your client is browsing to various web sites: google.com, salesforce.com, …, bad.com (oops). Standard routing cannot control this (well, I suppose I could load an entire black list and update it continuously, but that isn’t a realistic solution).With the cloud proxy you can control this at our edge device and force all HTTP and HTTPS traffic to be redirected to a filtering service in the cloud. This way you get the best of both worlds — ability to apply poicly without having to backhaul everything to corporate.Mike Carlton[I was part of the Pareto team that implemented this, now we’re busy integrating it into the Aerohive solution]